Vault Mode for private encrypted backups
by Jani on May 29th, 2022Update 05/2023: Vault Mode is now available!
One of our key design cornerstones is end-to-end encryption of our copies of your Google Photos Library, in transit and at-rest. This post describes how this is implemented at PhotoVaultOne, and how Vault Mode provides optional added privacy.
The following is a technical description of how Vault Mode is implemented. See this blog post for a non-technical description of how to use it.
There are several criteria that we always follow in our implementation of the security and privacy of your stored data:
- The implementation must provide strong isolation of stored content from one user to another.
- The underlying cryptography must be proven and standards based.
- There must be multiple overlapping layers of security, and a breach of one layer must not compromise all other layers.
- The architecture should be as cost efficient as possible, so that we can offer the service to you at an affordable rate.
Encryption of your photos and videos
Before we look at Vault Mode, let's first look at how encryption is implemented at PhotoVaultOne by default. We'll call this "normal mode".
In normal mode, the encryption of your our stored copy of your photos and videos is implemented as below: 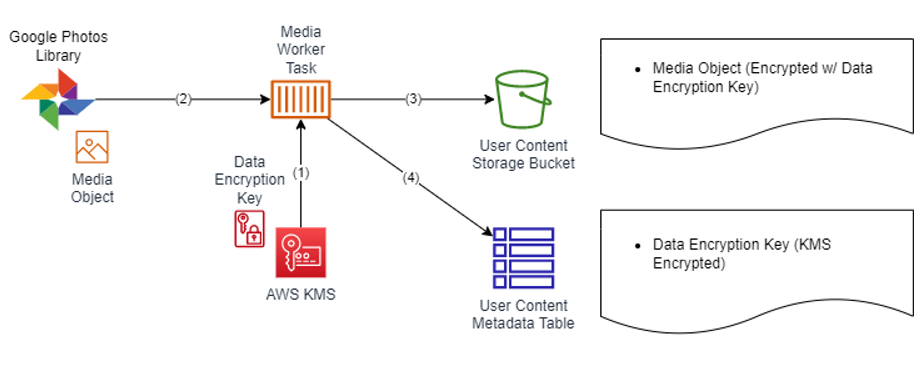
- A data encryption key (DEK) is generated using AWS KMS.
- A media object is downloaded from your Google Photos Library.
- The object is encrypted using the DEK. The encrypted object is stored in S3.
- The KMS ciphertext of the DEK is stored in the metadata table, so that the file can later be decrypted.
The use of so-called client-side encryption ensures that your images are never stored or exposed in plaintext, even if e.g a configuration error would expose the contents of the user content bucket.
Isolation of user data is ensured through the use of user-specific data encryption keys. For additional isolation, we utilize a mechanism in AWS KMS called EncryptionContext. This enables the use of additional authenticated data (AAD) in our cryptography operations. We provide your tenant-id (an internal identifier unique to you) as EncryptionContext for all KMS operations.
These are not our only user isolation mechanisms, but only the ones related to cryptography. We will write more about the other mechanisms at a future blog post.
Audit trail
Because the DEK is stored as a KMS ciphertext, it must always be decrypted using the KMS service before the associated media file can be decrypted. This provides an additional benefit, in that it provides an immutable audit trail of all access to your media files.
AWS KMS natively integrates with AWS Cloud Trail. We are able to rely on the AWS signed logs managed by the Cloud Trail service. These logs contain a trail of each KMS decrypt operation, and can be used to audit all access to all stored content. Importantly, this also provides us with a mechanism to prove that we never access any of our users' stored data.
Vault Mode for total privacy
As we saw earlier, already in normal mode all your files are client-side encrypted by PhotoVaultOne prior to storage in Amazon S3. We expect that the protection provided by normal mode is suitable for a broad range of our users. The most privacy-focused customers can additionally enable Vault Mode. We will next describe what is different in Vault Mode.
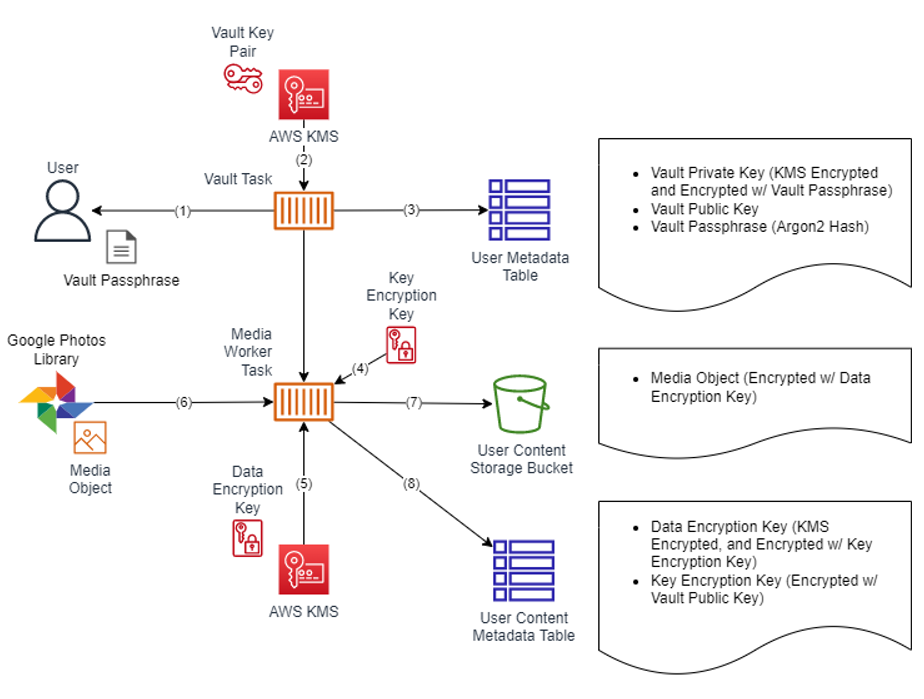
- The user activates Vault Mode, and receives a random 30-character vault key.
- A RSA key pair is generated for asymmetric encryption.
- a) An Argon2 hash of the vault key, b) the vault public key and c) a KMS ciphertext of the vault private key encrypted with the vault key are each persisted in your user information.
- A random key encryption key (KEK) is generated.
- (as before) A data encryption key (DEK) is generated using AWS KMS.
- (as before) A media object is downloaded from your Google Photos Library.
- (as before) The object is encrypted using the DEK. The encrypted object is stored in S3.
- The KMS ciphertext of the DEK is encrypted using the KEK, and stored in the metadata table. The KEK is encrypted using your vault public key, and also stored in the metadata table.
If Vault Mode is enabled, your data cannot be accessed or recovered without your vault key. You are responsible for safely storing the key.
Summary
Vault Mode provides absolutely privacy of your stored content through the use of asymmetric cryptography, and is designed for the most privacy-focused customers. We can continue to every day every day download and store your latest media files, and encrypt them using your public key. Only you can access your content, as your private key is protect by the vault key - known only by you.
About the author
Jani is the Founder and Chief Architect of PhotoVaultOne. Jani is also a Principal Solutions Architect at Amazon Web Services, where he strives to be a trusted advisor for Enterprises in the Nordics.
Disclaimer: All opinions and claims expressed are personal, and not that of Amazon Web Services.